Delete root access keys - Study guides, Class notes & Summaries
Looking for the best study guides, study notes and summaries about Delete root access keys? On this page you'll find 110 study documents about Delete root access keys.
Page 3 out of 110 results
Sort by

-
AWS Cloud Practitioner - A Cloud Guru PRACTICE EXAM Already Passed
- Exam (elaborations) • 9 pages • 2023
-
Available in package deal
-
- $9.49
- + learn more
AWS Cloud Practitioner - A Cloud Guru PRACTICE EXAM Already Passed Delete root access keys, activate MFA on root account, apply IAM password policy, use groups to assign permissions, create individual IAM users Best Practices for Securing Root AWS Account Federated Access To grant users access to AWS services with corporate directory User Authorized, then Autheniticated The order a user is granted access to AWS services Compliance with Laws & Regulations, Certifications/Attestations Componen...

-
CISA Domain 4 Exam 103 Questions with Verified Answers,100% CORRECT
- Exam (elaborations) • 17 pages • 2024
-
- $11.49
- + learn more
CISA Domain 4 Exam 103 Questions with Verified Answers Management - CORRECT ANSWER Plans, builds, runs and monitors activities in alignment with the direction set by the governance body to achieve the enterprise objectives. Is the responsibility of the executive management, under the leadership of the CEO IS Management - CORRECT ANSWER Ensuring that adequate resources are allocated to suport IS operations Planning to ensure the most efficient and effective use of an operation's resources...

-
CYSE 101 quiz & lab review Questions with correct Answers
- Exam (elaborations) • 11 pages • 2023
-
Available in package deal
-
- $18.49
- + learn more
CYSE 101 quiz & lab review Questions with correct Answers If we are using an 4-character password that contains only lowercase English alphabetic characters (26 different characters), how many more possible passwords are there if we use a 5-character password (still only lowercase English alphabetic characters? a. 11,424,400 more possibilities b. 26 more possibilities c. Same number of possibilities because still using lowercase English alphabetic characters d. 456,976 more possibilities...

-
CISA Exam 50 Question with Verified Answers,100% CORRECT
- Exam (elaborations) • 45 pages • 2024
-
- $10.99
- + learn more
CISA Exam 50 Question with Verified Answers Question: Asset Classification Information is one of an organization's most important assets. It should be considered when developing the organization's business and security objectives. It is much easier to map business and security objectives for a given information asset when assets are classified. What is the benefit of classifying information assets? Choose the best option(s) from those listed below. a) Establishing appropriate access co...

-
CompTIA CySA+ Final - Study Guide With Complete Solution
- Exam (elaborations) • 66 pages • 2023
- Available in package deal
-
- $13.49
- + learn more
Which format does dd produce files in? A. ddf B. RAW C. EN01 D. OVF - Answer B. dd creates files in RAW, bit-by-bit format. EN01 is the EnCase forensic file format, OVF is virtualization file format, and ddf is a made-up answer. Files remnants found in clusters that have been only partially rewritten by new files found are in what type of space? A. Outer B. Slack C. Unallocated space D. Non-Euclidean - Answer B. Slack space is the space that remains when only a portion of a cluster is...

-
PowerBI Certification Exam Prep 2024 latest update already graded A+
- Exam (elaborations) • 19 pages • 2024
-
- $15.49
- + learn more
What are some of the data sources you can use in PBI? Flat files & Folders (csv, text, excel, json, etc). Databases (SQL Access, Oracle, IBM, MySql, etc.). Power Platform (Dataflows, Power BI Datasets, Datavers3, etc). Azure (SQL Db, Blob Storage, Cosmos DB, Data Lake Storage, etc). Online Services (Sharepoint, Github, Dynamics 365, Google Analytics, Salesforce, etc). Others (web feeds, R scripts, Spark, Hadoop, etc.). What let's you shape and transform data? Query editor What is Po...
-
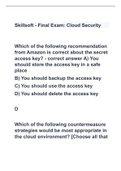
Skillsoft - Final Exam: Cloud Security with all correct answers
- Exam (elaborations) • 42 pages • 2023
-
Available in package deal
-
- $11.99
- + learn more
Which of the following recommendation from Amazon is correct about the secret access key? A) You should store the access key in a safe place B) You should backup the access key C) You should use the access key D) You should delete the access key D Which of the following countermeasure strategies would be most appropriate in the cloud environment? [Choose all that apply.] A) Avoid using the compensating controls B) Implement a redundant control for every control C) Use as much au...

-
SK0-004 CompTIA Server+ Practice Questions & ANSWERS ALL LATEST UPDATE 2023/24 EDITION GUARANTEED GRADE A+
- Exam (elaborations) • 129 pages • 2023
-
- $17.89
- + learn more
Which of the following is the height of 1U of space in a server rack? A. 1.5 inches (3.8 cm) B. 1.75 inches (4.4 cm) C. 2 inches (5.1 cm) D. 3 inches (7.6 cm) B A blade server chassis has two power supplies. Which of the following is a benefit of a technician connecting each power supply to a separate UPS unit? A. Quality of service B. Fault tolerance C. Traffic shaping D. Load balancing B A blade chassis can hold 16 half-height blades or eight full-height blades. Which of the fo...

-
CCNP and CCIE Security Core SCOR 350-701 - All Questions - Volume 1 ALL ANSWERS 100% CORRECT SOLUTION LATEST EDITION 2023 GUARANTEED GRADE A+
- Exam (elaborations) • 155 pages • 2023
-
- $20.29
- + learn more
AMP for Endpoints feature that allows you to create lists for Custom Detections, Application Control, Network, and Endpoint IOCs Outbreak Control File body-based signatures, MD5 signatures, and logical signatures are additional signature types supported by ____ Advanced custom detections Outbreak control IP lists can be used in conjunction with ____ detections, which can flag or even block suspicious network activity Device flow correlation (DFC) Types of exclusion sets available in AMP fo...

-
GOOGLE ASSOCIATE CLOUD ENGINEER EXAM | QUESTIONS & ANSWERS (VERIFIED) | LATEST UPDATE | GRADED A+
- Exam (elaborations) • 44 pages • 2024
-
- $14.49
- + learn more
1 GOOGLE ASSOCIATE CLOUD ENGINEER EXAM | QUESTIONS & ANSWERS (VERIFIED) | LATEST UPDATE | GRADED A+ What is the purpose of a VPC ? Correct Answer: Connects resources to each other and the internet. networks are ___ , subnets are ___ Correct Answer: global,regional How would you increase the size of a subnet? Correct Answer: expanding IP addresses What is the purpose of a pre-emptible VM? Correct Answer: permission to terminate if resources are needed elsewhere. Also very cheap ...

How much did you already spend on Stuvia? Imagine there are plenty more of you out there paying for study notes, but this time YOU are the seller. Ka-ching! Discover all about earning on Stuvia


