Exam (elaborations)
Palo Alto Module 2 with 100% correct answers already graded A|GUARANTEED SUCCESS
- Course
- Institution
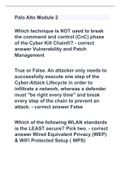
Which technique is NOT used to break the command and control (CnC) phase of the Cyber Kill Chain®? Vulnerability and Patch Management True or False. An attacker only needs to successfully execute one step of the Cyber-Attack Lifecycle in order to infiltrate a network, whereas a defender mu...
[Show more]